In the quiet hum of a server farm, in a place you may never see,…
Category: Technology
The Future of AI: 10 Predictions That Will Change Everything
Artificial Intelligence is no longer a whisper in the labs of computer scientists — it’s…
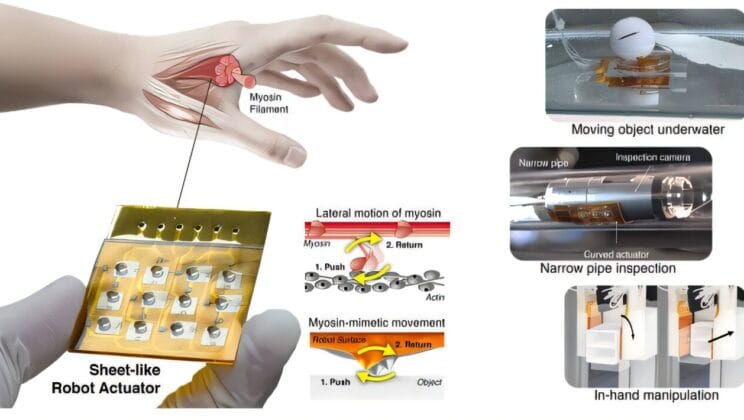
Paper Thin Robot Inspired by Human Muscle Could Change Surgery Forever
Robots have long been associated with rigid metal arms, powerful motors, and heavy industrial machinery.…
The AI Breakthrough Bringing Nikola Tesla’s Dream Back to Life
Over a century ago, Nikola Tesla envisioned a world where power flowed invisibly through the…
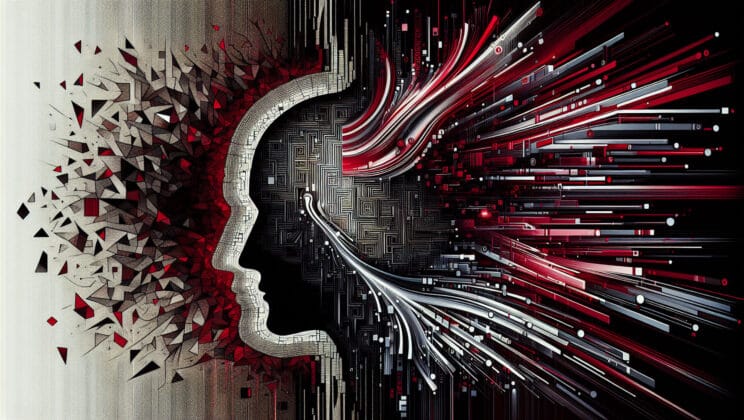
Scientists Discover a Way to Vaccinate AI Against Bad Behavior
Artificial intelligence is quickly becoming the co-worker none of us applied for but somehow ended…
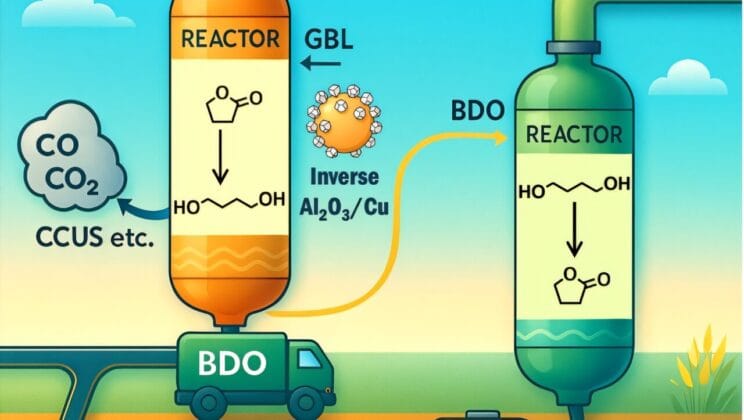
New Discovery Could Make Storing Hydrogen as Easy as Pumping Gasoline
Hydrogen has long been hailed as the fuel of the future — a clean, versatile…
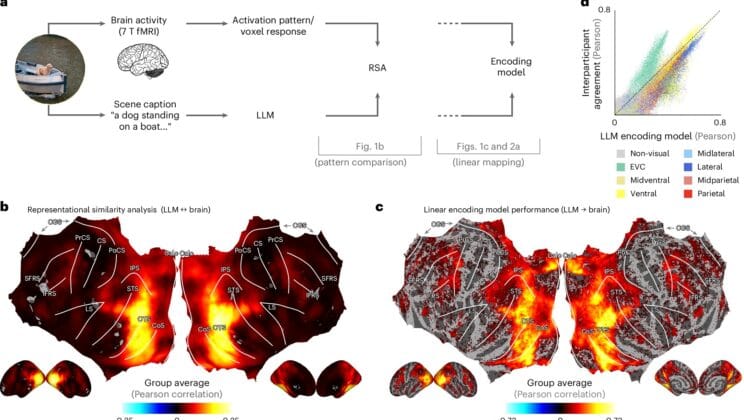
The Stunning Discovery That AI Understands the World Almost Like We Do
When you glance at a busy street corner, you don’t just notice “a car,” “a…
Scientists Create Fuel Cell That Runs Hotter Than a Coffee Maker Yet Powers the Future
In the global race to reduce carbon emissions and meet ever-growing energy demands, researchers are…
Scientists Create Self Healing Fuel Cell Powered by Artificial Intelligence
Fuel cells have long been hailed as one of the most promising clean-energy solutions of…
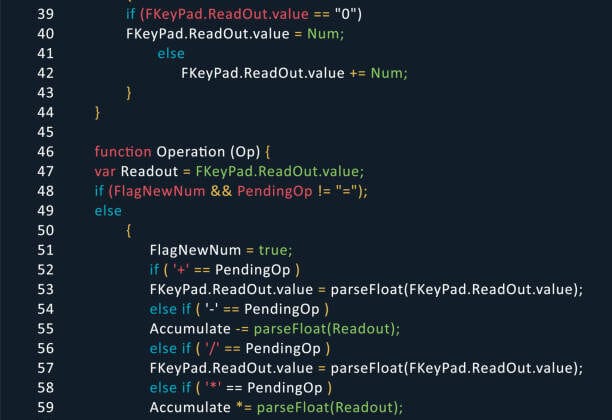
How to Start a Career as a Web Developer: A Complete Roadmap
Somewhere in the quiet hours of the night, you might be staring at your computer…
The 10 Best Programming Languages to Learn in 2025
Somewhere in the quiet hum of a coworking space, a developer leans back in their…
A Beginner’s Guide to Learning Python: The Most Versatile Language
If you were to walk into a room full of programmers from all corners of…
The Definitive Guide to Blockchain for Data Security
The internet promised connection, but it also birthed a paradox: the more connected we became,…
Cybersecurity vs. Data Privacy: Understanding the Key Differences
We live in an era where the invisible currents of data flow through every corner…
The Ultimate Guide to Zero-Trust Security Models
Imagine you’re in a medieval castle. Towering stone walls guard the perimeter, a heavy gate…
A Comprehensive Guide to Creating Strong and Memorable Passwords
Every day, billions of invisible conversations happen across the internet — your banking app confirming…
The History of Hacking: From ‘Phreakers’ to Nation-State Attacks
Long before “hacker” became a term whispered in corporate security briefings and splashed across sensational…
What is a VPN and Why Do You Need One?
The internet often feels like an invisible world that simply works. You open your phone,…
The 5 Best Cybersecurity Practices for Small Businesses
Picture this: it’s a quiet Tuesday morning. The coffee machine hums in the corner, your…
Understanding Phishing: A Guide to Spotting and Avoiding Scams
Imagine you’re walking along a quiet beach at sunrise. The waves are calm, the air…
How to Protect Your Privacy in the Age of Big Data
Imagine walking down a crowded city street. Every step you take, every glance at a…
The Essential Guide to Personal Cybersecurity for a Safer Digital Life
There’s a war going on right now, and you’re standing in the middle of it…