The internet often feels like an invisible world that simply works. You open your phone, tap a browser, type a question, and answers appear in seconds. Messages travel instantly across continents. Videos stream from servers thousands of miles away. Everything feels seamless, effortless, and private.
Yet beneath that smooth experience lies a complex web of connections, data transfers, and digital pathways. Every time you connect to the internet, your device sends information across networks owned by many different organizations. Your internet service provider routes your traffic, websites record your visits, and public Wi-Fi networks may expose your data to strangers sharing the same connection.
In this environment, privacy is not automatic. Security is not guaranteed. The internet was originally designed for openness and connectivity, not necessarily for personal privacy.
This is where the concept of a Virtual Private Network, widely known as a VPN, becomes important. A VPN is a technology that creates a secure, encrypted tunnel between your device and the internet. It acts like a protective layer between you and the networks you use, helping shield your activity from unwanted observation.
Understanding what a VPN is and why people use it requires exploring how the internet works, how data travels, and how privacy can be preserved in a connected world.
The Nature of Internet Connections
To understand a VPN, it helps to understand how normal internet connections operate. When you connect to a website, your device communicates with remote servers through a series of network nodes. These nodes include routers, data centers, and service providers that help move your data from one place to another.
Your internet service provider, commonly called an ISP, acts as the gateway between your home network and the broader internet. Every request you send to a website passes through this provider. In many cases, the provider can see which domains you access and when the requests occur.
When you visit a website, the site also receives certain information about your connection. This typically includes your IP address, a unique numerical label assigned to your internet connection. The IP address helps websites know where to send data back to you.
This process allows the internet to function efficiently, but it also means that your digital activity leaves traces. Data packets moving across networks can sometimes be observed by network operators or malicious actors, especially if the connection is not encrypted.
In many everyday situations this may not pose a serious problem, but in certain circumstances—such as public networks, sensitive communications, or restrictive digital environments—extra protection becomes valuable.
The Concept Behind Virtual Private Networks
A Virtual Private Network is designed to add a layer of security and privacy to internet connections. It creates an encrypted connection between a user’s device and a remote server operated by the VPN provider.
Instead of sending data directly from your device to the destination website, the VPN first routes the data through this secure tunnel. The encrypted data travels to the VPN server, which then forwards the request to the internet on your behalf.
To the outside world, it appears as if the request came from the VPN server rather than your personal device. Your real IP address is masked, and your internet traffic is protected by encryption while traveling through the tunnel.
Encryption is a fundamental concept in cybersecurity. It involves transforming readable information into encoded data using mathematical algorithms. Only authorized parties with the correct keys can decode the information back into its original form.
When a VPN encrypts your traffic, it ensures that anyone who intercepts the data packets cannot easily understand their contents.
This combination of encryption and rerouting is what gives VPNs their power.
The Meaning of “Virtual” and “Private”
The name Virtual Private Network reflects the way the technology functions.
The word “virtual” refers to the fact that the network connection does not require a physical dedicated cable between two points. Instead, it uses existing internet infrastructure to simulate a private connection.
The word “private” reflects the security and confidentiality provided by encryption and authentication. Even though the data travels through public networks, it remains protected from unauthorized access.
The term “network” refers to the connection created between your device and the VPN server, which functions as a secure gateway to the internet.
Together, these elements create a system that mimics the security of a private network while operating over the global internet.
The Role of Encryption in VPN Technology
Encryption is the foundation of VPN security. Without encryption, data traveling across the internet can potentially be intercepted or analyzed by third parties.
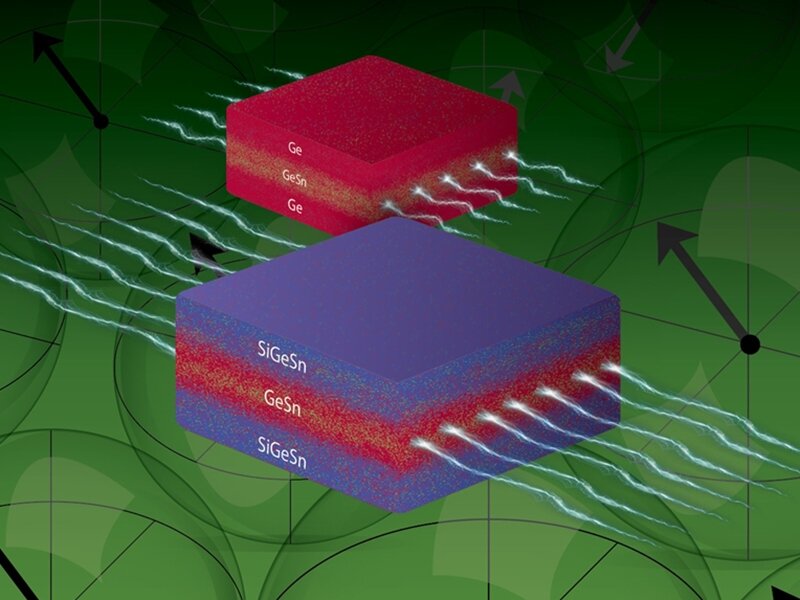
Modern VPNs typically rely on advanced cryptographic protocols that use complex mathematical operations to secure communications. These systems transform readable data into encrypted code that cannot be understood without the appropriate decryption key.
Many VPN technologies use protocols such as OpenVPN, WireGuard, or Internet Protocol Security to establish secure connections.
Each protocol provides methods for authentication, encryption, and secure data transmission. They ensure that even if data packets are captured while traveling across networks, the information remains protected.
Encryption algorithms themselves often rely on standards such as Advanced Encryption Standard, a widely trusted method used across modern cybersecurity systems.
These technologies work together to create a shield around internet traffic.
Why Public Wi-Fi Can Be Risky
Public Wi-Fi networks are one of the main reasons people consider using VPNs. These networks are commonly found in airports, cafes, hotels, and libraries, providing convenient internet access to anyone nearby.
However, public networks are typically shared by many users and may lack strong security protections. Because multiple devices connect to the same network, attackers may attempt to intercept data transmissions or create fake access points to trick users into connecting.
When your device connects to an unsecured network, your data can potentially be monitored if it is not encrypted. Sensitive information such as login credentials, personal messages, or financial details could be exposed.
A VPN helps reduce this risk by encrypting your data before it leaves your device. Even if someone attempts to intercept the data on the network, they would see only encrypted information rather than readable content.
In environments where network security cannot be guaranteed, this extra protection becomes particularly valuable.
Privacy in the Age of Data Collection
The modern internet economy relies heavily on data. Websites collect information about visitors in order to improve services, deliver targeted advertisements, and analyze user behavior.
While many forms of data collection are legitimate and transparent, others raise concerns about privacy. Tracking technologies such as cookies and digital fingerprints can build detailed profiles of online behavior.
Because your IP address can reveal approximate location and internet provider, it becomes one of the identifiers that websites may record.
When using a VPN, the IP address visible to websites belongs to the VPN server rather than your device. This helps reduce the ability to directly link online activity to your personal connection.
It is important to note that VPNs do not make a person completely anonymous online. Websites can still use other tracking methods, and user behavior can still reveal identity in many cases. However, VPNs significantly reduce the exposure of network-level information.
In a digital landscape where personal data is often valuable, additional privacy tools can provide greater control over what information is shared.
Access to Global Content
Another reason people use VPNs is related to the geographic structure of the internet. Some online content is restricted based on location. This practice, known as geo-blocking, occurs when websites limit access to users from certain regions.
Geo-blocking can occur for several reasons. Licensing agreements, regulatory restrictions, or regional distribution rights may determine where certain digital content can be accessed.
Because a VPN routes your connection through servers located in different countries, it can allow your internet traffic to appear as if it originates from those locations. This may enable access to services or information that would otherwise be unavailable in a particular region.
While this capability is widely discussed in relation to entertainment streaming platforms, the broader concept involves how digital borders exist on the internet.
VPN technology demonstrates that physical location and digital presence do not always have to align.
Security for Remote Work
The rise of remote work has increased the importance of secure network connections. Employees often need to access company systems, internal databases, or confidential files while working outside traditional office environments.
Organizations frequently use VPN technology to create secure access to internal networks. When employees connect to the corporate VPN, their devices become part of a protected network environment.
This ensures that sensitive information travels through encrypted channels and that only authorized users can reach internal systems.
Corporate VPNs are often managed by company IT departments, ensuring strict authentication procedures and security policies. These systems allow businesses to maintain security even when employees work from homes, shared offices, or while traveling.
VPNs and the Evolution of Cybersecurity
The concept of virtual private networks emerged in the late 20th century as organizations sought ways to securely connect remote offices and employees to internal networks.
Instead of building expensive dedicated communication lines, companies realized they could use the public internet while protecting data through encryption. This innovation allowed secure communication without the cost of private physical infrastructure.
Over time, VPN technology evolved from enterprise networking tools into widely available consumer privacy services. Today many individuals use VPN applications on smartphones, laptops, and tablets to enhance their personal online security.
As cyber threats and digital surveillance concerns have grown, VPNs have become part of a broader ecosystem of cybersecurity tools.
Limitations and Misconceptions
While VPNs provide important benefits, they are not a universal solution to every online security challenge. Understanding their limitations is essential for realistic expectations.
A VPN protects data in transit between your device and the VPN server, but it does not eliminate all risks. Malware infections, phishing attacks, and unsafe downloads can still compromise devices regardless of VPN use.
Additionally, users must trust the VPN provider itself. Because internet traffic passes through the provider’s servers, the company operating the service technically has access to connection metadata. Reputable providers address this concern through transparency policies and minimal data retention practices.
Another misconception is that VPNs guarantee complete anonymity. True anonymity requires multiple layers of privacy protection and careful digital behavior. A VPN primarily focuses on encrypting traffic and masking IP addresses.
Understanding both the strengths and limits of VPN technology helps users apply it effectively.
The Science of Secure Communication
At its core, VPN technology relies on principles from computer science, mathematics, and network engineering. Encryption algorithms depend on complex number theory and computational difficulty to protect data.
Protocols governing VPN communication manage authentication, data integrity, and error correction. Network routing ensures data packets reach the correct destinations efficiently.
The reliability of these systems depends on careful engineering and constant research in cybersecurity. Advances in computing power and cryptographic analysis continuously shape how encryption methods evolve.
Scientists and engineers work to ensure that modern encryption remains resistant to attacks even as technology advances.
The Human Desire for Privacy
Beyond the technical aspects, the popularity of VPNs reflects something deeply human: the desire for privacy.
Privacy allows individuals to explore ideas, communicate freely, and access information without constant observation. In physical spaces, people naturally expect personal boundaries. Online environments raise new challenges because data can be easily recorded and analyzed.
Tools like VPNs attempt to restore some of that balance by giving users more control over how their information travels through digital networks.
In many ways, the debate around online privacy mirrors earlier historical discussions about personal rights, freedom of expression, and technological change.
The Future of VPN Technology
As the internet continues to evolve, VPN technology will likely adapt alongside it. Emerging developments such as quantum computing, advanced encryption methods, and new internet protocols may reshape how secure communication works.
Some researchers explore ways to integrate stronger privacy protections directly into internet infrastructure. Others develop decentralized networking models that distribute control more widely.
Regardless of the specific technologies that emerge, the underlying challenge remains the same: balancing connectivity with security.
VPNs represent one chapter in that ongoing effort.
Understanding the Digital Shield
When people ask what a VPN is, the simplest answer is that it is a secure tunnel for internet traffic. But that description captures only the surface of a much larger idea.
A VPN represents the intersection of privacy, mathematics, cybersecurity, and the architecture of the internet. It reflects a recognition that digital communication requires protection just as physical spaces do.
Every message sent, every website visited, every piece of information transferred across networks travels through systems that can potentially expose it. A VPN adds a layer of encryption and redirection designed to reduce that exposure.
In an increasingly connected world, where billions of devices communicate across vast digital highways, tools that safeguard information have become essential.
A VPN does not make the internet perfect or completely private. Yet it offers something valuable: a measure of control over how your data moves through the invisible pathways of the online world.
And in the age of constant connectivity, that control can make a meaningful difference.