The modern world runs on invisible threads of information. Every message sent, every bank transaction completed, every photograph shared, and every piece of knowledge searched online travels through digital pathways that connect billions of people across the planet. This immense web of communication and data has transformed civilization in ways that would have been unimaginable just a few decades ago. Yet within this powerful digital universe lies a constant challenge: protecting information from those who seek to steal, manipulate, or destroy it.
Cybersecurity is the discipline devoted to defending computers, networks, systems, and data from digital threats. It is both a science and a strategy, combining technology, human awareness, and carefully designed systems to protect the integrity of the digital world. In simple terms, cybersecurity is about keeping information safe in an age where information has become one of the most valuable resources on Earth.
Behind every secure website, protected bank account, encrypted message, and safe corporate network stands an intricate system of safeguards designed to prevent unauthorized access. These safeguards form the backbone of cybersecurity. They protect not only personal privacy but also national infrastructure, global commerce, and the stability of modern society.
Cybersecurity is not merely a technical field reserved for experts working behind computer screens. It touches nearly every aspect of daily life. The security of your smartphone, the protection of medical records, the reliability of online shopping platforms, and the defense of government systems all depend on cybersecurity principles.
As humanity moves deeper into a digital age, understanding cybersecurity becomes essential for individuals, businesses, and governments alike.
The Digital Revolution and the Rise of Cyber Threats
The roots of cybersecurity lie in the rapid expansion of computing technology. In the early days of computers, systems were isolated machines used mainly by researchers, engineers, or government institutions. Security concerns existed, but they were limited in scope because computers rarely communicated with each other.
This situation changed dramatically with the emergence of global computer networks and the development of the internet. When interconnected systems began exchanging vast amounts of information, new vulnerabilities appeared. Data traveling across networks could be intercepted, altered, or stolen.
The creation of the modern internet is often associated with the pioneering work of organizations such as ARPANET, which laid the technological foundation for global digital communication. As networks grew larger and more complex, the opportunities for malicious activity expanded as well.
Cyber threats evolved alongside technological progress. Early forms of computer misuse involved simple experimentation or curiosity. Over time, however, cyber attacks became more organized and sophisticated. Criminal groups recognized the financial potential of digital theft, while political actors realized the strategic value of cyber espionage.
Today, cyber threats can originate from individual hackers, criminal organizations, corporate spies, extremist groups, or even nation-states. These threats target everything from personal information to national infrastructure systems.
The growing dependence on digital technology has made cybersecurity one of the most critical challenges of the twenty-first century.
Understanding the Core Goals of Cybersecurity
At the heart of cybersecurity lies a set of principles designed to protect digital information and systems. These principles guide the design of security technologies and strategies.
The first essential goal is confidentiality. Confidentiality ensures that sensitive information is accessible only to authorized individuals or systems. Personal messages, financial records, medical histories, and classified government documents all require strong protection against unauthorized access.
Another crucial objective is integrity. Integrity ensures that data remains accurate and unaltered during storage or transmission. If attackers could modify financial records or scientific data without detection, the consequences could be catastrophic. Maintaining data integrity ensures that information remains trustworthy.
The third fundamental goal is availability. Availability ensures that systems and data remain accessible when needed. Cyber attacks that disable services, such as distributed denial-of-service attacks, threaten availability by overwhelming systems with traffic or disrupting infrastructure.
Together, confidentiality, integrity, and availability form the foundational framework guiding cybersecurity practices. These principles help ensure that digital systems remain reliable, trustworthy, and secure.
The Nature of Cyber Threats
Cyber threats take many forms, each exploiting weaknesses in software, networks, or human behavior. Some threats focus on stealing information, while others aim to disrupt operations or cause damage.
Malicious software, often known as malware, represents one of the most common categories of cyber threats. Malware includes viruses, worms, spyware, ransomware, and trojans—each designed to infiltrate systems and perform harmful actions.
Viruses attach themselves to legitimate programs and spread when those programs are executed. Worms replicate independently across networks, spreading rapidly without human intervention. Spyware secretly collects information about users, often capturing passwords or browsing behavior.
Ransomware has become particularly notorious in recent years. This type of malware encrypts a victim’s files and demands payment in exchange for restoring access. Hospitals, corporations, and government agencies have all been targeted by ransomware attacks.
Phishing represents another widespread threat. In phishing attacks, cybercriminals impersonate legitimate organizations through emails or messages to trick individuals into revealing sensitive information. A convincing message appearing to come from a bank or online service may persuade victims to disclose passwords or financial details.
Social engineering attacks exploit human psychology rather than technological weaknesses. Attackers manipulate trust, fear, or urgency to persuade people to grant access or share confidential data.
Cyber threats continue to evolve as attackers develop new techniques to bypass security measures.
How Cybersecurity Protects Systems
Cybersecurity relies on multiple layers of protection to defend against threats. No single solution can guarantee complete security. Instead, effective protection requires a combination of technologies, policies, and user awareness.
Encryption plays a central role in protecting digital communication. Encryption converts readable information into encoded data that can only be deciphered using a specific key. Even if attackers intercept encrypted data, they cannot easily understand it without the correct key.
Secure authentication systems help verify the identity of users attempting to access systems. Passwords remain the most common form of authentication, but modern cybersecurity increasingly relies on multi-factor authentication. This approach requires users to provide additional proof of identity, such as a temporary code sent to a mobile device or biometric verification like a fingerprint.
Firewalls act as digital gatekeepers for networks. They monitor incoming and outgoing traffic, allowing legitimate communication while blocking suspicious activity.
Intrusion detection systems analyze network activity to identify unusual behavior that might indicate an attack. When suspicious activity is detected, security teams can respond quickly to prevent further damage.
Software updates and security patches are also essential. Developers frequently discover vulnerabilities in software systems. Regular updates ensure that these weaknesses are corrected before attackers can exploit them.
Cybersecurity operates as an ongoing process rather than a one-time solution.
The Human Factor in Cybersecurity
Despite advanced technologies, humans remain the most unpredictable element in cybersecurity. Many successful cyber attacks occur not because of technical flaws but because individuals unknowingly grant access to attackers.
A single weak password, careless click on a malicious link, or failure to update software can open the door to significant breaches. Cybersecurity therefore emphasizes education and awareness.
Organizations often conduct training programs to teach employees how to recognize suspicious emails, protect sensitive information, and follow safe digital practices. Individuals are encouraged to create strong passwords, avoid sharing personal data on insecure platforms, and remain cautious when interacting with unfamiliar online sources.
The intersection of human behavior and digital systems makes cybersecurity both a technical and psychological challenge.
Cybersecurity and the Global Economy
The digital economy depends heavily on cybersecurity. Online banking, e-commerce platforms, financial markets, and digital payment systems process enormous volumes of sensitive data every day.
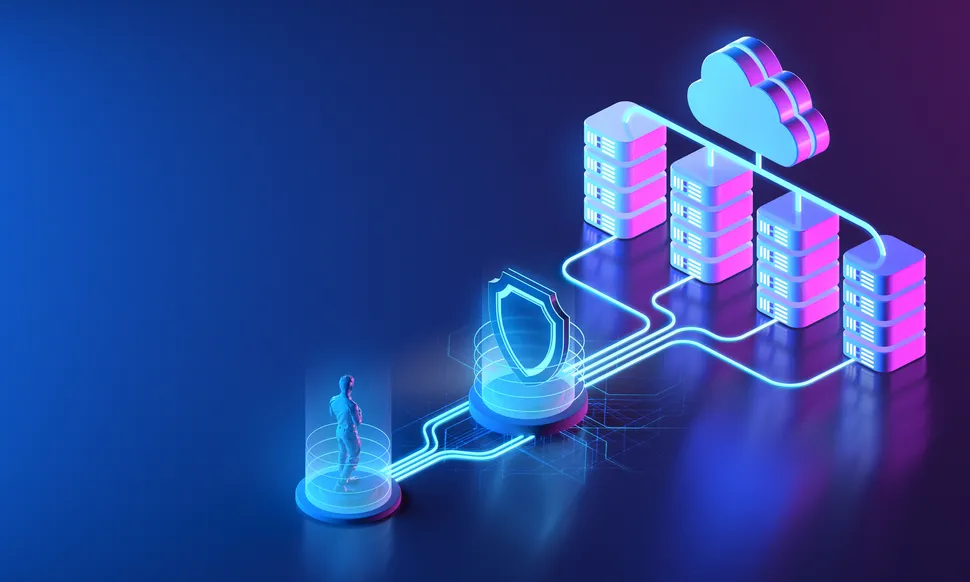
Companies such as Amazon, Google, and Microsoft operate massive cloud infrastructures that store and process data for millions of users worldwide. Protecting these systems from cyber threats is critical to maintaining trust and stability in the global economy.
Cybercrime has grown into a multi-billion-dollar industry. Stolen credit card numbers, personal identities, and confidential corporate data can be sold on underground digital markets. Organized criminal networks operate sophisticated operations designed to exploit vulnerabilities in financial systems.
The financial consequences of cyber attacks extend far beyond direct theft. Data breaches can damage a company’s reputation, reduce consumer trust, and lead to significant legal penalties.
For governments, cybersecurity is equally important. National security increasingly depends on protecting digital infrastructure such as energy grids, transportation systems, and communication networks.
Cybersecurity in Government and National Defense
In the modern geopolitical landscape, cyberspace has become a new domain of conflict. Nations invest heavily in cyber defense capabilities to protect critical infrastructure and sensitive government data.
Cyber espionage operations seek to steal technological secrets, military plans, and diplomatic communications. Some cyber attacks target essential services such as electricity, water systems, or transportation networks, potentially disrupting entire societies.
Government agencies dedicated to cybersecurity play a central role in defending national digital infrastructure. Organizations like National Security Agency and Cybersecurity and Infrastructure Security Agency focus on monitoring threats and coordinating defensive measures.
The rise of cyber warfare has prompted international discussions about digital conflict and the need for global cooperation in establishing cybersecurity norms.
Emerging Technologies and New Security Challenges
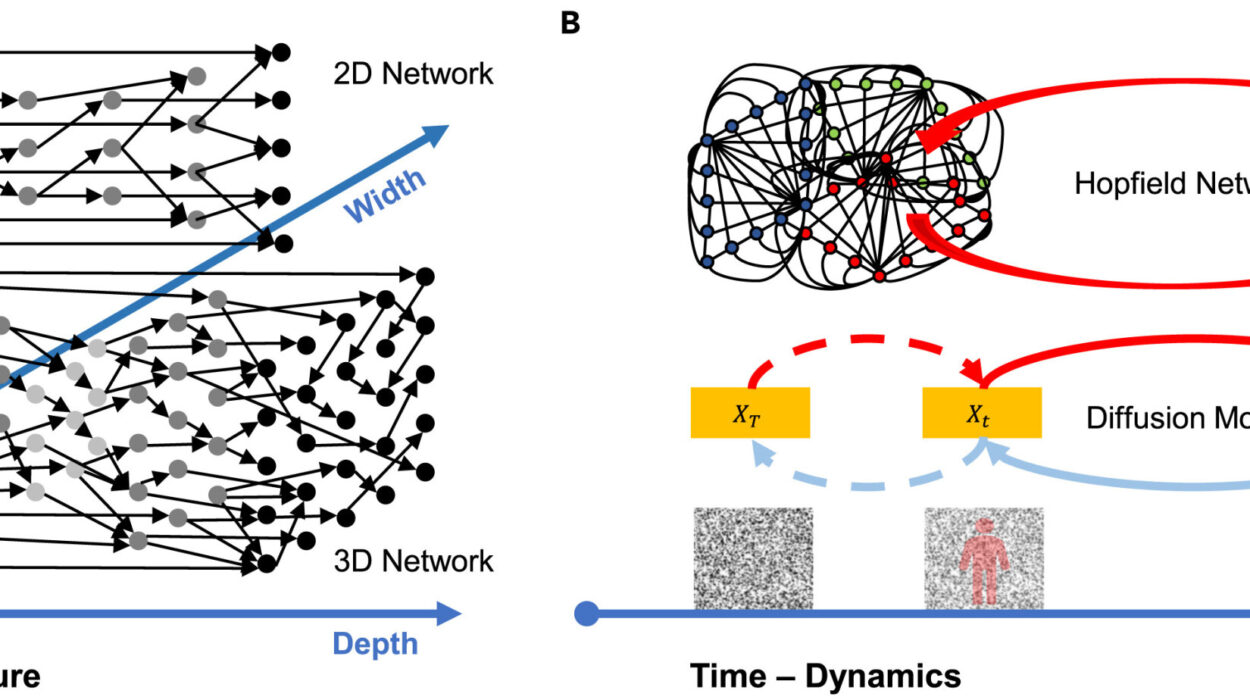
Technological innovation continuously reshapes the cybersecurity landscape. Emerging technologies create both opportunities and new vulnerabilities.
Cloud computing has revolutionized how organizations store and process data. Instead of maintaining physical servers on-site, companies can access computing resources remotely through internet-based platforms. While cloud services offer flexibility and scalability, they also require robust security measures to protect shared infrastructure.
The Internet of Things has introduced billions of connected devices into homes and industries. Smart thermostats, wearable health monitors, industrial sensors, and autonomous vehicles all rely on network connectivity. Each connected device represents a potential entry point for cyber attackers if not properly secured.
Artificial intelligence is beginning to influence cybersecurity in profound ways. AI systems can analyze vast amounts of data to detect patterns of malicious behavior more quickly than human analysts. At the same time, attackers may also use AI to develop more sophisticated cyber attacks.
Quantum computing represents another emerging challenge. Traditional encryption methods rely on mathematical problems that are extremely difficult for classical computers to solve. Quantum computers may eventually possess the ability to break certain types of encryption, prompting researchers to develop new forms of quantum-resistant cryptography.
Cybersecurity must continually adapt to keep pace with these technological transformations.
The Future of Cybersecurity
The future of cybersecurity will likely involve deeper integration between technology, policy, and human awareness. As digital systems become more complex, security strategies will increasingly rely on automation, artificial intelligence, and global collaboration.
International cooperation may become essential in combating cybercrime, as attacks frequently cross national borders. Governments, corporations, and research institutions will need to share information and coordinate responses to emerging threats.
Education will also play a crucial role. The next generation of engineers, computer scientists, and policymakers must develop the skills necessary to design secure systems and manage evolving digital risks.
Cybersecurity is not a static field. It is a dynamic and constantly evolving discipline shaped by the creativity of both defenders and attackers.
Why Cybersecurity Matters to Everyone
It is easy to imagine cybersecurity as a distant concern affecting only large corporations or government agencies. In reality, it affects every individual who uses digital technology.
Personal data stored on smartphones, social media accounts, email platforms, and online banking services represents valuable targets for cybercriminals. Identity theft, financial fraud, and privacy violations can have serious consequences for individuals.
Protecting personal information requires vigilance and responsible digital behavior. Simple practices such as enabling multi-factor authentication, using secure networks, and maintaining updated software can significantly reduce risk.
Ultimately, cybersecurity is about trust. It ensures that digital systems remain reliable and safe, allowing people to communicate, learn, conduct business, and innovate without constant fear of intrusion.
The Continuing Journey of Digital Protection
Cybersecurity represents one of the defining challenges of the digital age. As technology reshapes the world, safeguarding information becomes essential to preserving economic stability, personal privacy, and national security.
The field stands at the intersection of science, technology, human behavior, and global cooperation. It demands creativity, vigilance, and constant adaptation.
Every new device connected to the internet, every new application developed, and every new technological breakthrough introduces fresh possibilities and new vulnerabilities. Cybersecurity must evolve alongside these changes, anticipating threats before they emerge.
The story of cybersecurity is still unfolding. It is the story of humanity learning to protect the digital universe it has created—a universe built not of atoms and stars, but of code, networks, and information.
And as our world grows ever more connected, the guardians of that digital universe will become more important than ever before.