In the world of artificial intelligence, few innovations have captured both imagination and impact as…
The Future of AI Regulation: What Policymakers Are Considering
Artificial intelligence has advanced from a futuristic concept to an integral part of modern life,…
What Are Capsule Networks? Next-Gen Neural Network Architectures Explained
Deep learning has revolutionized artificial intelligence, giving rise to machines capable of recognizing faces, translating…
What Is Zero-Shot Learning? Understanding Models That Generalize Better
In the ever-expanding landscape of artificial intelligence and machine learning, the capacity to generalize beyond…
What Is the Cyber Kill Chain? Understanding Attack Phases
In the realm of cybersecurity, understanding how attacks unfold is just as critical as developing…
GDPR, CCPA and Global Data Privacy Laws: What You Should Know
Data has become the currency of the digital age. Every time a person browses a…
What Is Social Engineering? The Psychology Behind Cyber Attacks
In the world of cybersecurity, technological defenses often take center stage—firewalls, encryption, intrusion detection systems,…
The Future of Passwordless Authentication
For decades, passwords have been the foundation of digital security, acting as the gateway to…
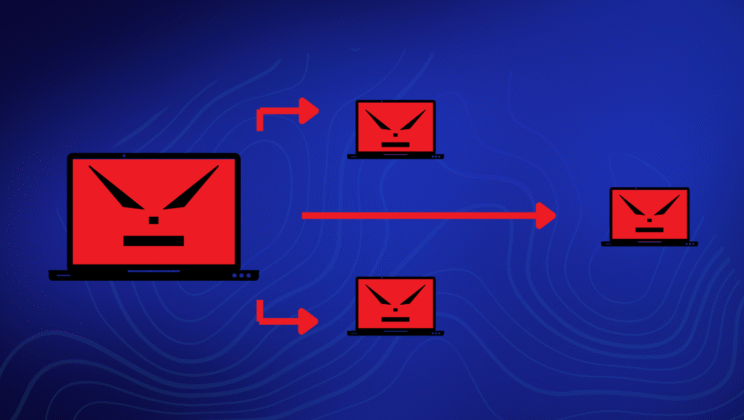
What Are Botnets and How Do They Work?
In the hidden corners of the internet, a silent digital army operates ceaselessly—millions of infected…
What Are Supply Chain Attacks and How to Mitigate Them
In today’s interconnected digital ecosystem, cybersecurity is no longer confined within the walls of a…
The Importance of Two-Factor Authentication (2FA)
In the digital age, where personal information, financial data, and professional assets are deeply integrated…
How to Recognize and Avoid Online Scams
The internet has transformed the way humanity communicates, shops, learns, and does business. But beneath…
How to Secure Your Personal Devices from Hackers
In the digital era, personal devices such as smartphones, laptops, tablets, and even smart home…
Malware vs. Viruses: What’s the Difference?
In the vast and complex world of cybersecurity, few terms are as widely used—and as…
Denial-of-Service (DoS) Attacks: What You Need to Know
In the interconnected digital world, where data and services flow seamlessly across continents, the ability…
10 Common Cyber Attacks and How to Prevent Them
In the modern digital world, cyber threats have evolved into one of the most serious…
How Does Phishing Actually Work?
Phishing is one of the most pervasive and damaging forms of cybercrime in the modern…
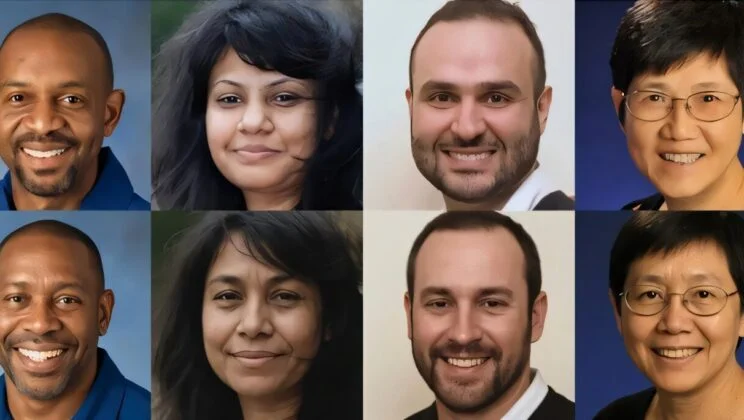
AI Can Now Fake Celebrity Photos So Perfectly That Even Experts Can’t Tell They’re Fake
A face has always been one of the most powerful symbols of truth. For centuries,…
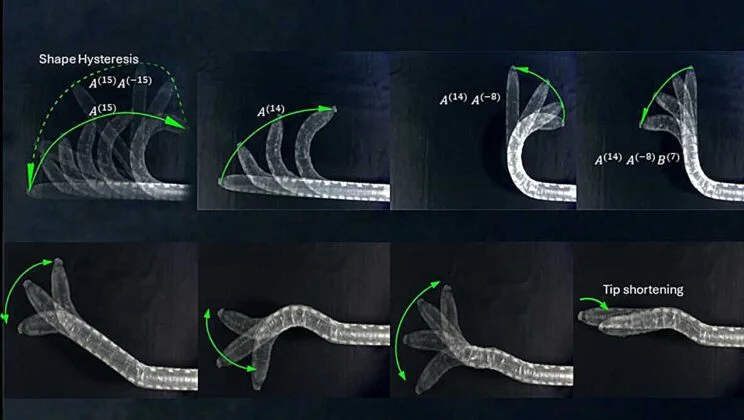
Meet the Robot That Can Remember Its Shape—and Move Like It’s Alive
For decades, engineers have been trying to make robots move more like living creatures—fluid, flexible,…
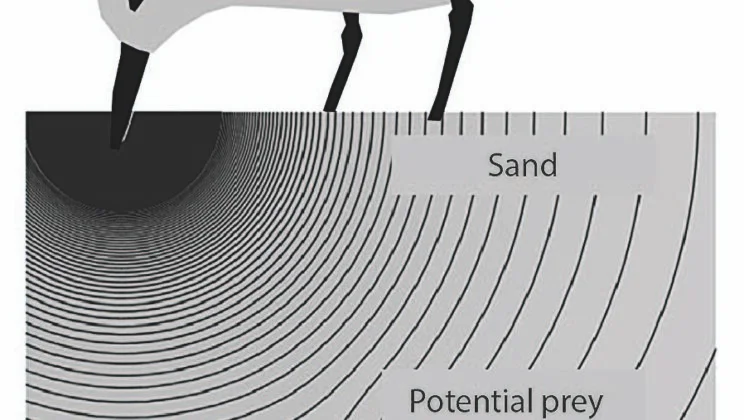
Humans Can “Feel” Objects Without Touching Them—New Study Reveals Hidden Sixth Sense
Imagine reaching into a box of sand and somehow feeling that something is hidden inside—without…
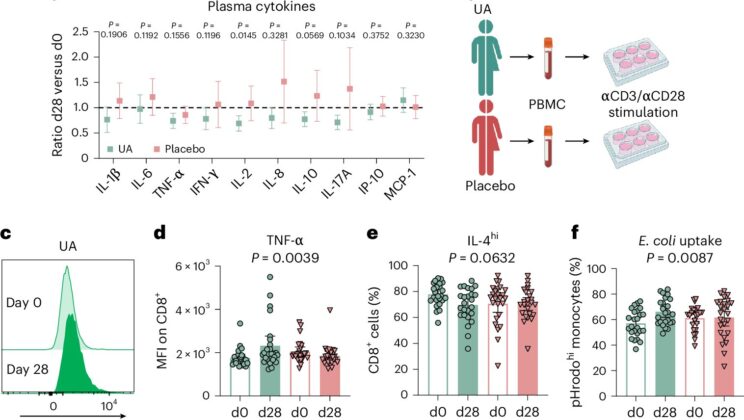
Scientists Discover Compound in Pomegranates That May Rejuvenate the Aging Immune System
Aging is inevitable—but what if some aspects of it could be slowed, or even gently…
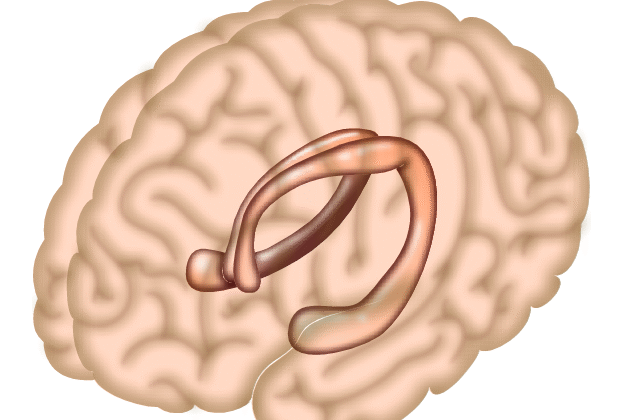
Scientists Discover How Friendship Literally Rewires Your Brain for Better Memory
It has long been said that humans are social creatures—that we thrive on connection, conversation,…