In the ever-expanding landscape of artificial intelligence and machine learning, the capacity to generalize beyond known data is the hallmark…
Category: Science & Technology
What Is the Cyber Kill Chain? Understanding Attack Phases
In the realm of cybersecurity, understanding how attacks unfold is just as critical as developing defenses to prevent them. Modern…
GDPR, CCPA and Global Data Privacy Laws: What You Should Know
Data has become the currency of the digital age. Every time a person browses a website, installs an app, or…
What Is Social Engineering? The Psychology Behind Cyber Attacks
In the world of cybersecurity, technological defenses often take center stage—firewalls, encryption, intrusion detection systems, and sophisticated algorithms designed to…
The Future of Passwordless Authentication
For decades, passwords have been the foundation of digital security, acting as the gateway to our personal data, financial systems,…
What Are Botnets and How Do They Work?
In the hidden corners of the internet, a silent digital army operates ceaselessly—millions of infected computers connected together, executing the…
What Are Supply Chain Attacks and How to Mitigate Them
In today’s interconnected digital ecosystem, cybersecurity is no longer confined within the walls of a single organization. Every company depends…
The Importance of Two-Factor Authentication (2FA)
In the digital age, where personal information, financial data, and professional assets are deeply integrated into online systems, the concept…
How to Recognize and Avoid Online Scams
The internet has transformed the way humanity communicates, shops, learns, and does business. But beneath its vast network of convenience…
How to Secure Your Personal Devices from Hackers
In the digital era, personal devices such as smartphones, laptops, tablets, and even smart home systems have become central to…
Malware vs. Viruses: What’s the Difference?
In the vast and complex world of cybersecurity, few terms are as widely used—and as commonly misunderstood—as “malware” and “virus.”…
Denial-of-Service (DoS) Attacks: What You Need to Know
In the interconnected digital world, where data and services flow seamlessly across continents, the ability to access online resources is…
10 Common Cyber Attacks and How to Prevent Them
In the modern digital world, cyber threats have evolved into one of the most serious dangers facing individuals, businesses, and…
How Does Phishing Actually Work?
Phishing is one of the most pervasive and damaging forms of cybercrime in the modern digital landscape. It operates through…
The Future of the Internet: Software, AI, and the Quantum Web
The internet is the nervous system of the modern world. It connects billions of people, powers global economies, and fuels…
What Is Firmware and How Does It Power Your Devices?
Firmware is one of the most essential yet least understood components of modern technology. It operates silently behind the scenes,…
Understanding Zero Trust Architecture in Modern Software
In the rapidly evolving digital landscape, security has become one of the most critical concerns for organizations and governments worldwide.…
Understanding Kubernetes: The Engine Behind Cloud Scalability
Kubernetes has become one of the most transformative technologies in modern computing, driving the global shift toward scalable, resilient, and…
What Is Continuous Integration and Why It Matters
Continuous Integration, commonly referred to as CI, is one of the most transformative practices in modern software development. It represents…
Waterfall vs. Agile vs. DevOps: The Great Software Debate
In the ever-evolving landscape of software engineering, three paradigms stand out as milestones in how humanity builds technology: Waterfall, Agile,…
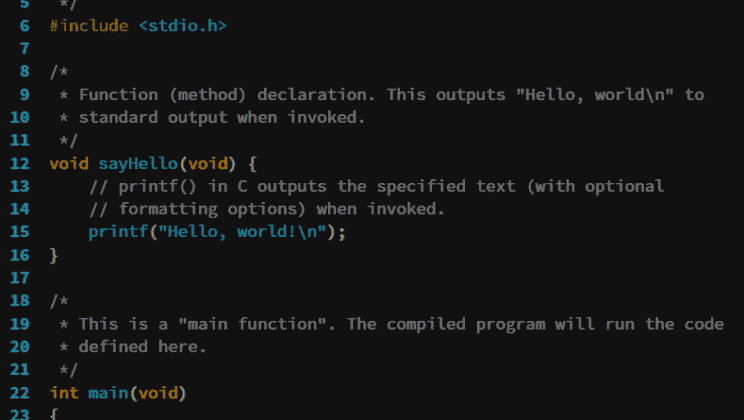
How to Choose the Right Programming Language for Your Project
Choosing the right programming language is one of the most important decisions in any software development project. It influences every…
What Is Software Engineering? A Look Inside the Developer’s Mind
Software engineering is both an art and a science—a discipline that merges creative problem-solving with rigorous logical thinking to design…