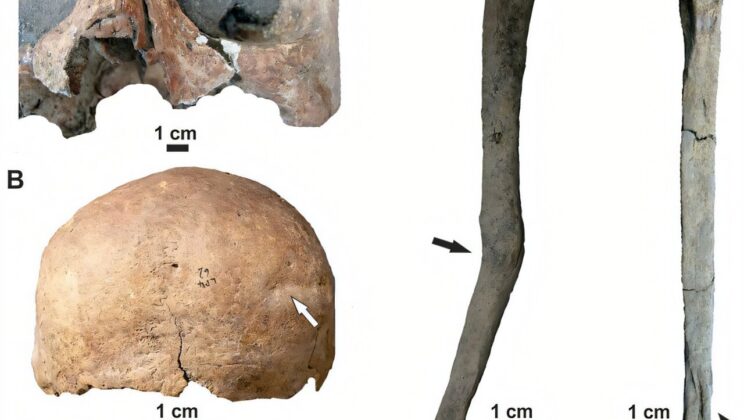
More than four thousand years ago, long before cities rose and written words captured history,…
Archaeologists Uncover 3,000-Year-Old Ritual Sites That Reveal the True Birthplace of Chinese Civilization
Long before the First Emperor of China raised his mighty armies and declared the unification…
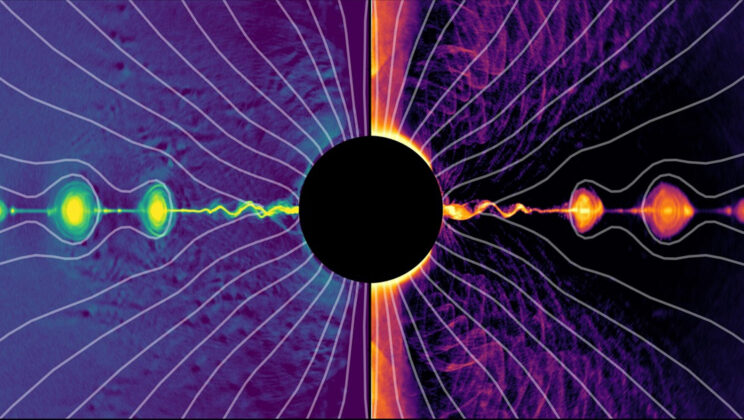
Scientists Finally Crack the Mystery of How Black Holes Create Light from Darkness
In 1918, long before humanity had even dreamed of photographing a black hole, astronomer Heber…
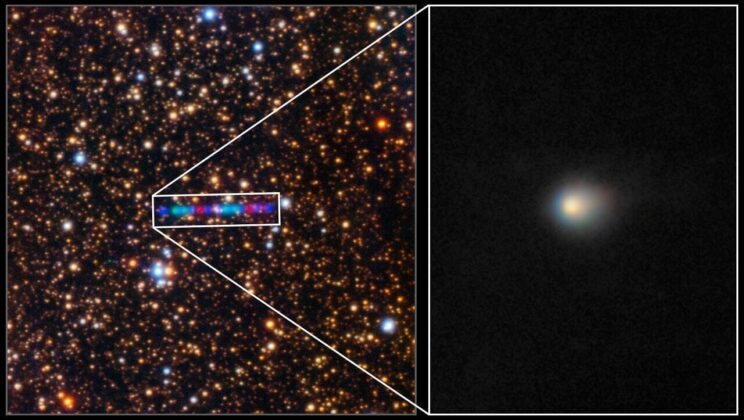
Scientists Stunned as Alien Comet 3I/ATLAS Begins Morphing Inside Our Solar System
Every so often, the universe sends us a visitor — a wanderer from the deep…
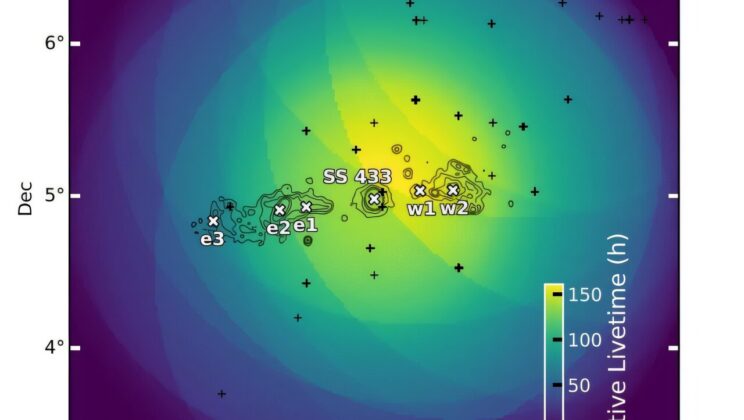
This Mysterious Star System Is Firing Energy Beams at Near-Light Speed — Scientists Finally Know Why
Across the dark expanse of our galaxy, invisible engines hum with unimaginable power. These are…
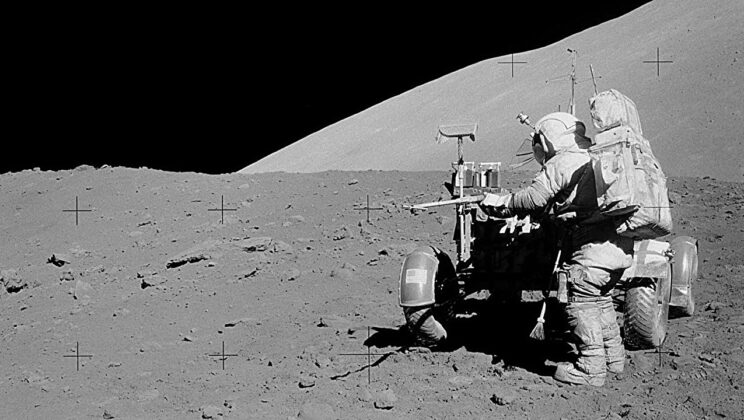
Scientists Opened a 50-Year-Old Moon Sample — And Found Something That Shouldn’t Exist
In December 1972, as astronauts Eugene Cernan and Harrison Schmitt prepared to leave the moon’s…
Birds: Evolution, Flight, and the Secret Lives of the Sky
There are moments in life when time seems to stop—a sudden hush before dawn, a…
15 Animal Superpowers Backed by Science
The world is full of extraordinary creatures, each carrying within them powers so astonishing they…
10 Animals With Incredible Regeneration Abilities
Life on Earth is defined by impermanence. Every creature, from the smallest insect to the…
10 Strange Animal Facts You Won’t Believe Are True
The natural world is full of mysteries—some breathtaking, some bizarre, and many so astonishing they…
10 Animals That Changed How We Understand Evolution
When Charles Darwin first set sail aboard The Beagle in 1831, he could not have…
10 Creatures Living in the Harshest Places on Earth
The Earth is not a gentle planet. Beneath its beauty lies brutality—scorching deserts, frozen wastelands,…
15 Animals That Hibernate in Extreme Ways
When winter descends and the world quiets beneath blankets of snow or the harsh breath…
10 Polar Animals Endangered by Climate Change
At the edges of the Earth, where sunlight glitters off endless sheets of ice and…
12 Heat-Resistant Desert Creatures
The desert is not a place of death—it’s a kingdom of miracles. Beneath the blistering…
10 Deep-Frozen Animals That Can Come Back to Life
Imagine a world locked in ice—a world where the pulse of life slows to near…
12 Animals That Can Survive Without Water
Water is the essence of life — the shimmering thread that binds every living being…
10 Weird Insect Defense Mechanisms
The world of insects is a universe of ingenuity, full of creatures so small they…
10 Amazing Pollinators Beyond Bees
When most people think of pollination, the first image that flutters to mind is that…
10 Fastest Insects in the World
Speed is one of nature’s most thrilling expressions of survival. When we think of speed,…
10 Animals That Thrive in the Arctic
The Arctic — a place where winter reigns most of the year, where temperatures plunge…
15 Most Colorful Beetles in Nature
Beneath the fallen leaves of rainforests, within the bark of ancient trees, and even in…